Dealing with Insider Threats
Charles Herring
17 March 2014
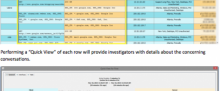
The most dangerous and difficult risk to detect to an organization is insider threat. When a trusted asset decides to betray the trust of his benefactor for the sake of ideology, greed or extortion the organization can suffer long lasting damage. This article outlines the nature and strategies of handling insider threat.