GrrCON 2024 - Birthing Perjury-free AI
Abstract
Cybersecurity analysis leading to deterrence of cybercrime requires processing thousands to billions of digital signals per second. Those signals must be accurately comprehended, forensically preserved then used to detect and investigate potential cybercrime. The work products must not only assist the investigators but must be translated into language that non-technical lay audiences including judges, lawyers and jurors can understand.
This presentation explores how generative artificial intelligence (GenAI), natural language processing (NLP), graph-theory and artificial narrow intelligence (ANI) can play a role in delivering these outcomes.
The session includes demonstrations of opensource toolkits, datasets and models designed to assist in this work.
Machine Learning Driven Social Engineering
2020 Conference & Security Meeting Talks
Last year, I spoke at 26 security meetings and conferences. I learn the most when I’m in the field with my heroes. If you have a local meeting or conference that would benefit from any of these topics, let us know and I’ll do my best to show up.
Metric Driven Development Presentations
From IIA/ISACA IT Hacking Conference : Developing software that changes the world, exceeds customer expectations, provides turn-key functionality in diverse scenarios while meeting security and compliance requirements is the holy grail of Security Development Operations (SECDEVOPS). There are thousands of variables that need to be constantly addressed to find the balance that delivers sustainable and secure success. In this session, WitFoo’s chief engineers will outline an innovative approach to secure devops called Metric Driven Development.
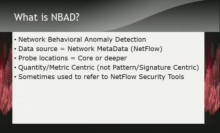
Breaking NBAD & UEBA Talk
From DEFCON & GrrCON: Network Behavior Anomaly Detection (NBAD) and User and Entity Behavior Analytics (UEBA) are heralded as machine learning fueled messiahs for finding advanced attacks. The data collection and processing methodologies of these approaches create a series of new exploitable vectors that can allow attackers to navigate network and systems undetected. In this session, methods for poisoning data, transforming calculations and preventing alerts will be examined. Proof of concept code will be demonstrated and made available. Approaches to harden against these attacks will also be discussed as well as outlining needed changes in detection standards.
GA ISSA Talk: People > Machines
I am looking forward to speaking at the Georgia Annual ISSA Meeting on 11/15. The blog series that the talk is based on is below.
GrrCon Presentation
Converge Conference Presentation
My presentation deck from Converge Conference can be downloaded here.